Technology
DDoS – What is it and how can you protect yourself
DDoS attacks are an escalating problem that affects millions of people every year. A DDoS attack happens when a hacker attempts to bring your website down with overwhelming traffic and causes the server to crash. DDoS attacks are one of the most powerful and devastating forms of cyber assault in existence.
The attacker can launch the attacks without significant resources, making it a real concern for organizations that use internet access to connect to customers.
The only way to protect yourself is through mitigation services or installing protection tools within your website.
What is DDoS?
Distributed denial of service or DDoS is a cyberattack where multiple systems flood the bandwidth or resources of a targeted system. A DDoS attack attempts to make an online service unavailable to its users by overwhelming it with traffic from multiple sources.
DDoS attacks come in various forms, from an email flood of messages sent to a large number of recipients to more complicated attacks that involve thousands of systems, called botnets.
Why DDoS Attacks?
A DDoS attack can target any website or web application. Still, the most common targets are online services (like websites), online games, banks and financial institutions, e-commerce websites, computer servers, and VoIP infrastructures.
There are many reasons behind a DDoS attack. Some of them are:
- Defacement of a website or webspace
- To demonstrate that the website/server is not secure enough from attacks
- To spread malware
- The hackers may be protesting against something, or they may be trying to get attention for themselves
- To gain unauthorized access to sensitive data
- To make money by blackmailing the server owner
- For political purposes
- Hacking competition between hackers and penetration testers
Types of DDoS Attacks
The main types of DDoS attacks are:
HTTP Flooding: It involves sending HTTP requests to overload a web server and cause it to become unavailable. The more complex the website, the greater the requests are needed to take it down. These types of attacks can be performed by anyone who has access to an Internet connection.
Slowloris: A type of DoS attack that involves opening many connections to a target server but never sending any data. Slowloris causes the server to become overloaded and unable to respond to legitimate requests.
Session Hijacking: The act of taking over an existing session between two systems, such as when a user logs into an account and another person uses the same account to log in later. The attacker can access information or make changes in the system without the user’s knowledge.
Cross-Site Request Forgery (CSRF) – a user clicks on a link that performs an unauthorized action.
How Can You Protect Yourself Against DDoS Attacks
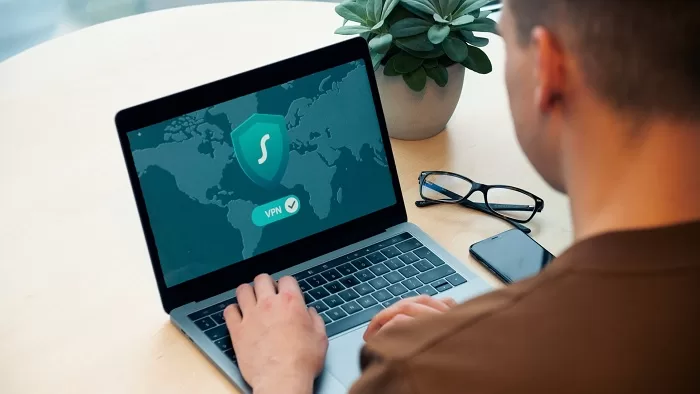
VPN
A VPN encrypts your Internet connection and prevents malicious third parties from monitoring your online activity or stealing your information. The attacker normally sends forged packets that include the victim’s IP address as the source IP address. To prevent DDoS attacks, you can get dedicated IP using VPN encryption that prevents hackers from seeing the websites you visit and blocks them from knowing what you do online in general. VPNs also provide an additional layer of security, which can help prevent hackers from remotely controlling your computer. VPN networking technology allows you to create a secure connection over a less-secure network.
Vulnerability Assessment
An effective way of fighting a DDoS attack is knowing what you’re up against. Vulnerability assessment is the process of testing the network for potential vulnerabilities that could lead to an outage or data loss. You can perform a vulnerability assessment manually or with assessment software.
Look out for red flags of imminent attacks.
Look out for red flags indicating an imminent DDoS attack. These could include an increase in spam or phishing emails, large fluctuations in website traffic, slowdowns or other unusual behavior on your website, or any failure of your systems to function as they normally would. If you see any of these indicators, take precautions to protect yourself against an imminent attack.
Preparation for possible attacks
A sure step in fighting a DDoS attack is preparing for it and learning how to spot one when it happens. Most DDoS attacks typically involve one or more of the following symptoms:
- Your network performance slows down during peak hours
- Your website becomes slow and unresponsive, causing you to lose potential customers
- You can’t log into your servers or devices
- An attacker makes contact via email usually and asks for a ransom payment in exchange for lifting the attack
Final Submission
Today, the number of DDoS attacks has increased because they’re easier to put together than ever before. In addition, criminals are increasingly using DDoS attacks not just as a smokescreen for other types of criminal activity but as extortion tools.